Table 1 from Intrusion detection systems (IDS) & future challenges in cloud based environment | Semantic Scholar
Sensors | Free Full-Text | An Optimization Model for Appraising Intrusion-Detection Systems for Network Security Communications: Applications, Challenges, and Solutions





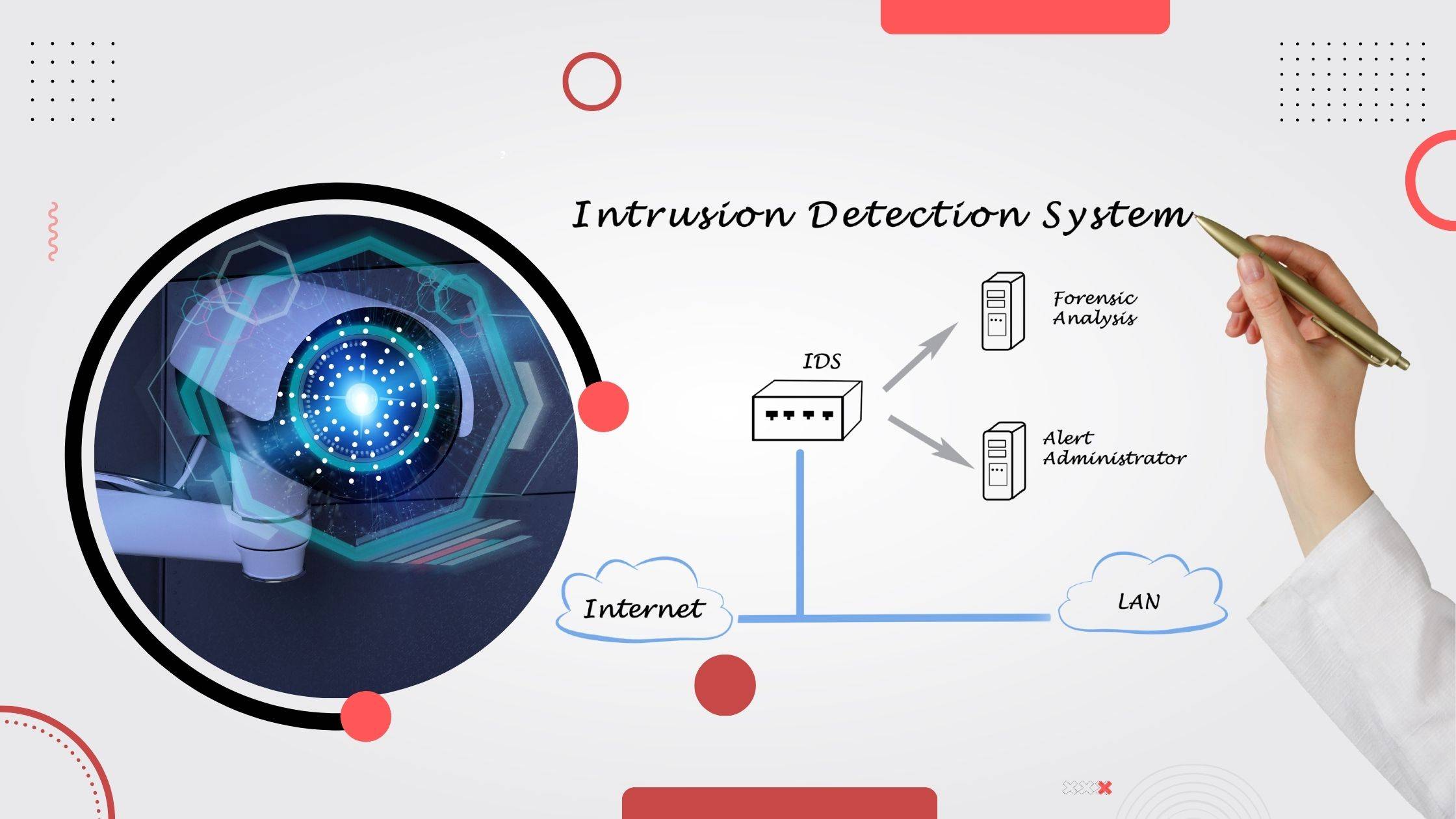

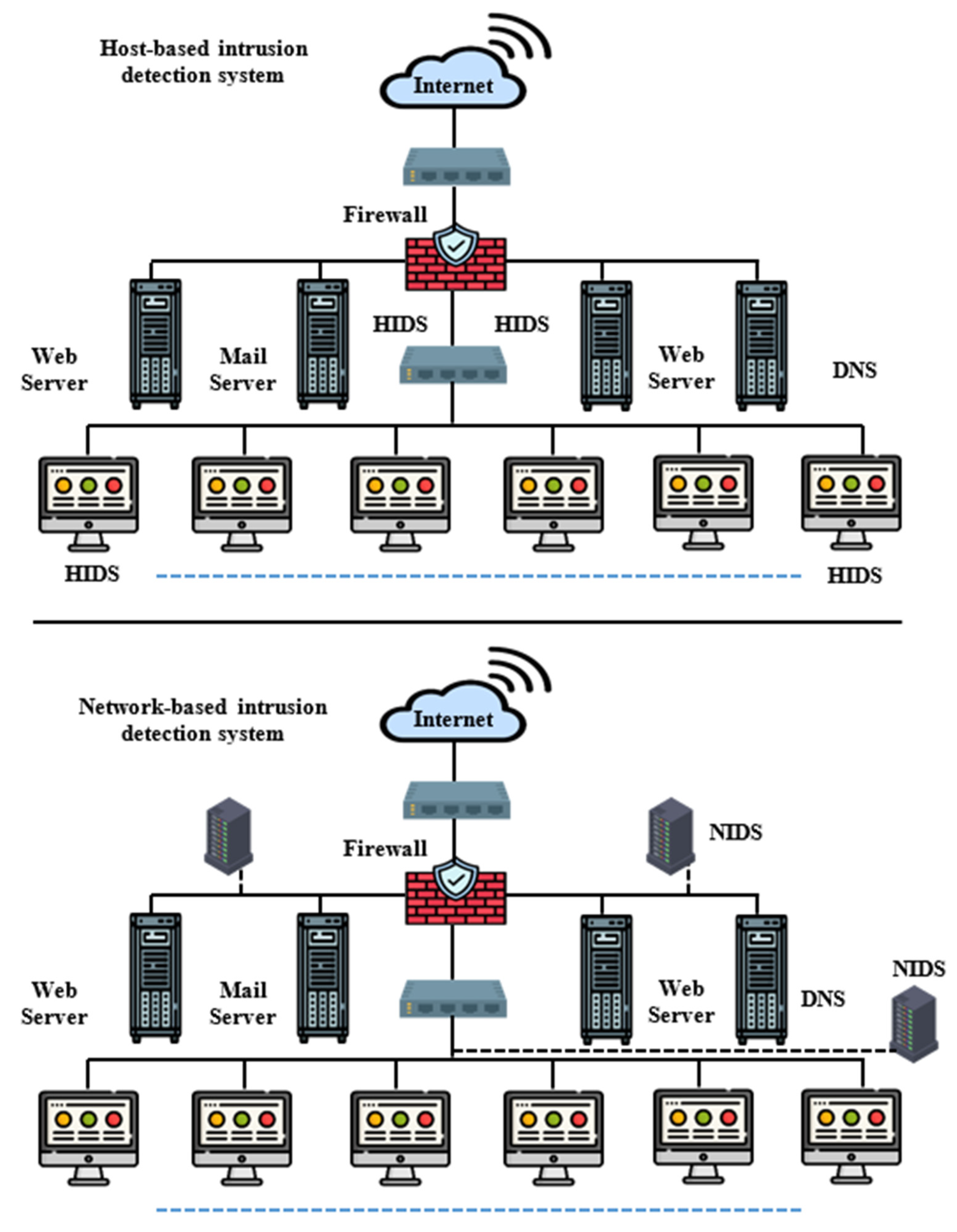
![Types of Intrusion Detection System (HIDS, NIDS, DIDS, IDPS) [13] | Download Scientific Diagram Types of Intrusion Detection System (HIDS, NIDS, DIDS, IDPS) [13] | Download Scientific Diagram](https://www.researchgate.net/publication/360979225/figure/fig1/AS:11431281122809197@1677553654237/Types-of-Intrusion-Detection-System-HIDS-NIDS-DIDS-IDPS-13.png)