
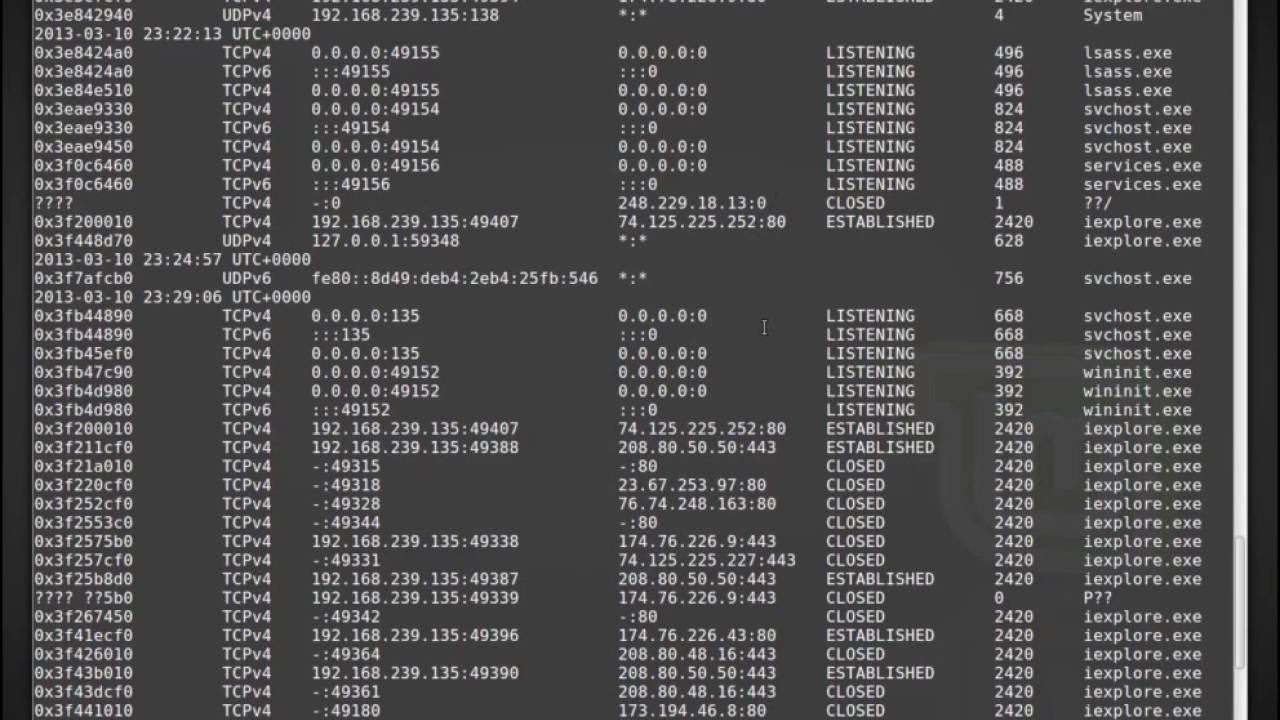
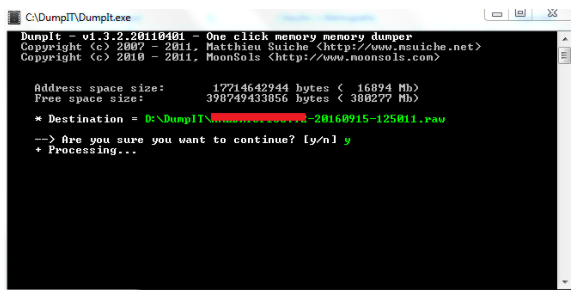
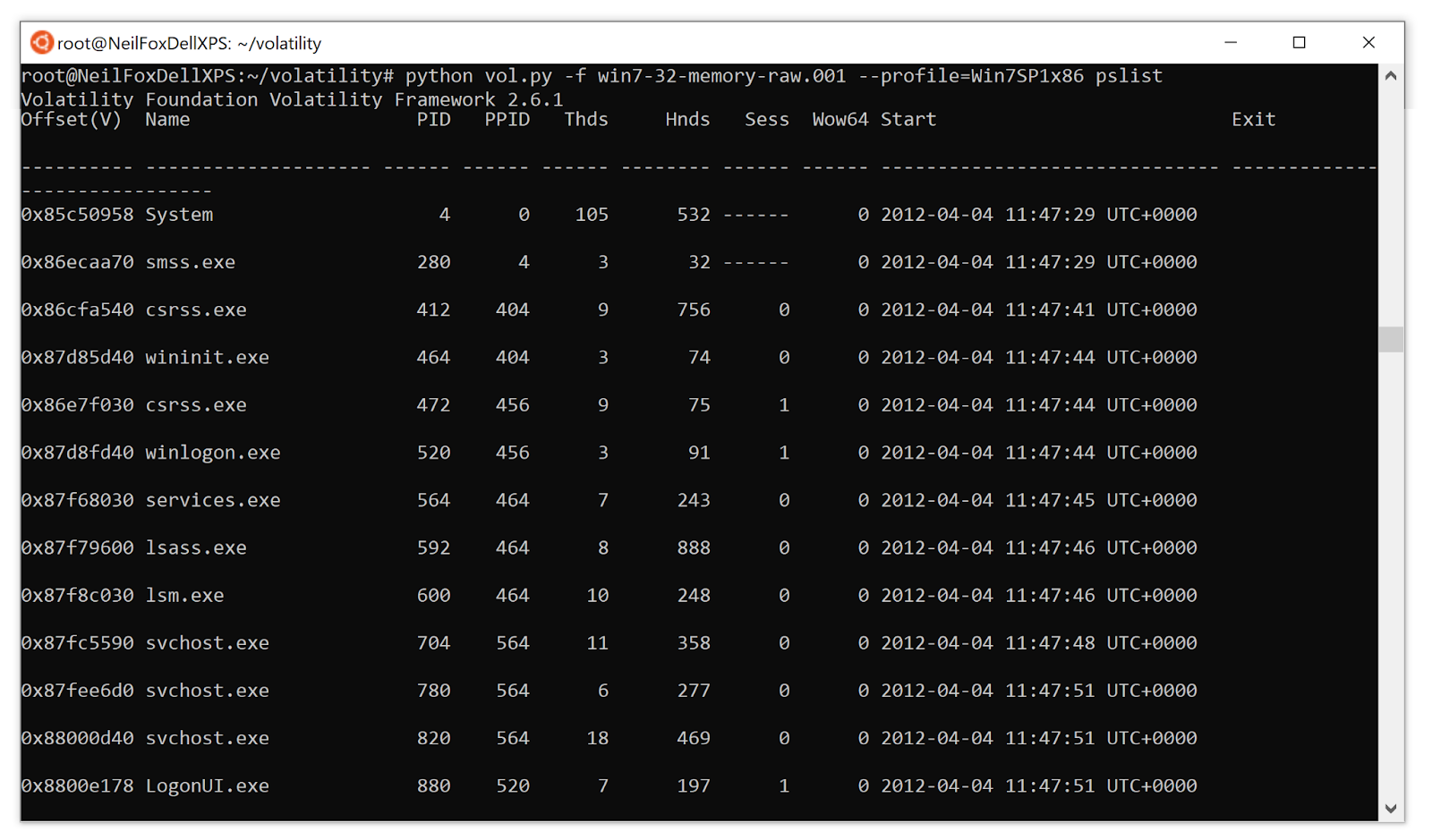
Hack Like a Pro: Digital Forensics for the Aspiring Hacker, Part 14 (Live Memory Forensics) « Null Byte :: WonderHowTo
Digging up memories – a deep-dive into memory forensics in the Cyber Security Essentials meetup | Nixu Cybersecurity.

The Art of Memory Forensics: Detecting Malware and Threats in Windows, Linux, and MAC Memory : Ligh, Michael Hale, Case, Andrew, Levy, Jamie, Walters, Aaron: Amazon.it: Libri

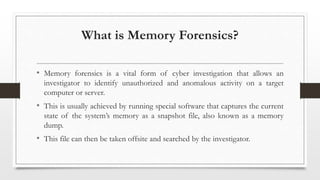
Signature based volatile memory forensics: a detection based approach for analyzing sophisticated cyber attacks | International Journal of Information Technology









![Memory Forensics | Windows Forensics [FREE COURSE CONTENT] - eForensics Memory Forensics | Windows Forensics [FREE COURSE CONTENT] - eForensics](https://eforensicsmag.com/wp-content/uploads/2022/08/Course-content.png)

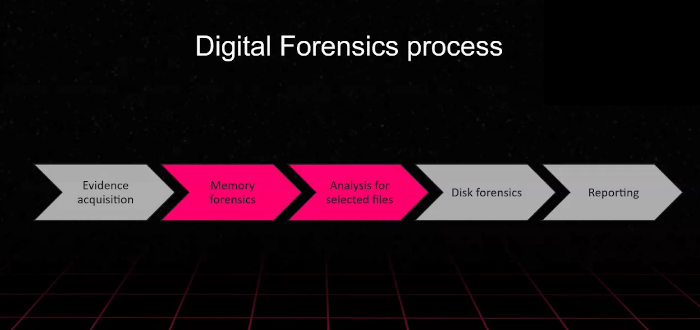
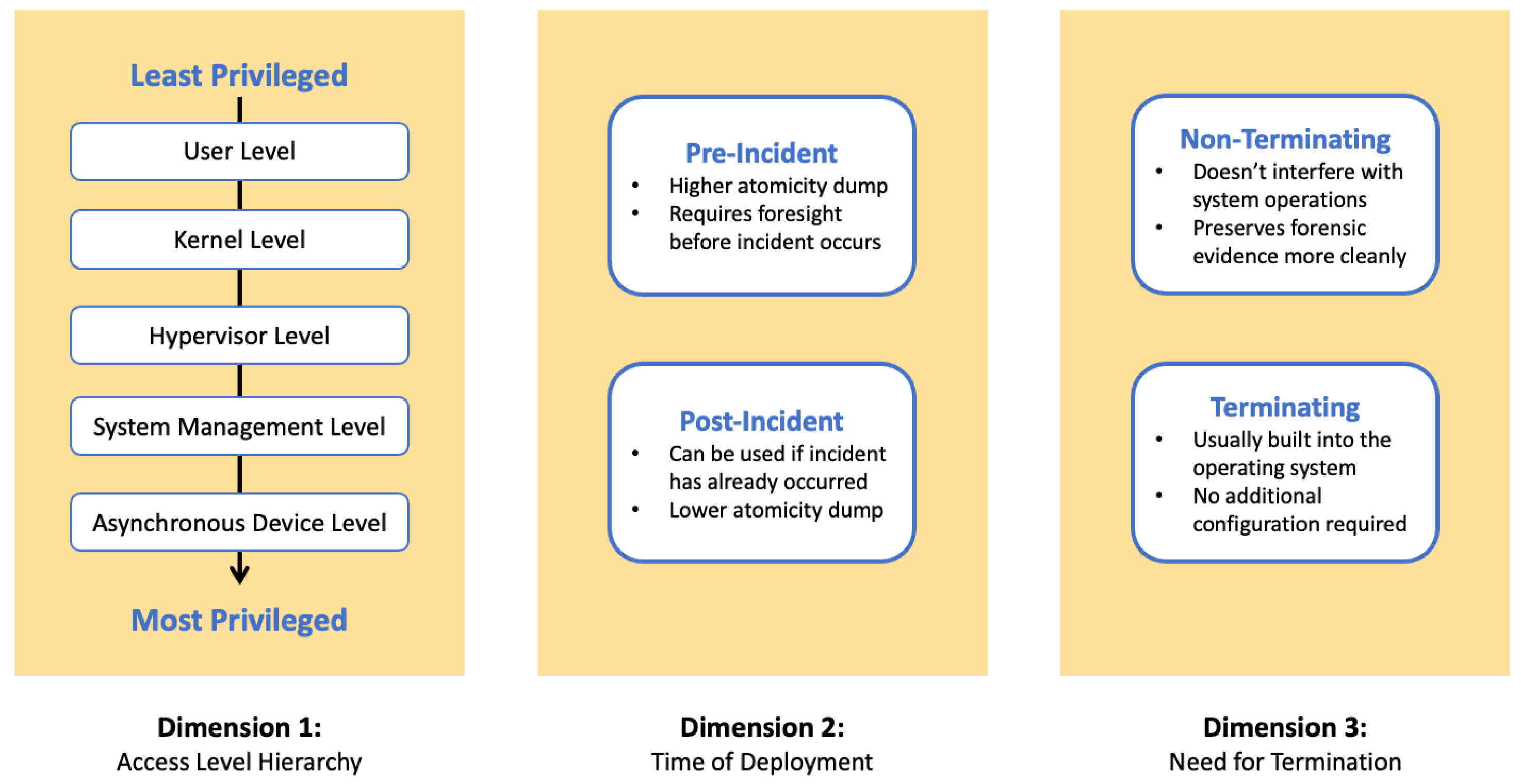
![PDF] Memory Forensics: Review of Acquisition and Analysis Techniques | Semantic Scholar PDF] Memory Forensics: Review of Acquisition and Analysis Techniques | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/5844da2c4456091748958bcc035ff8a52e6d8340/18-Figure1-1.png)