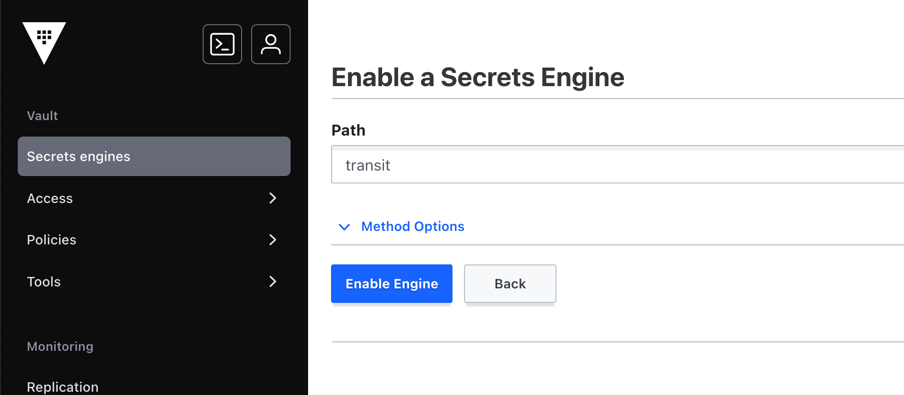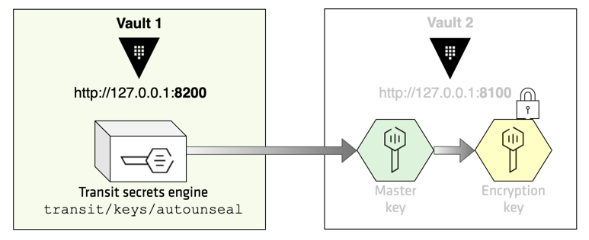
Docker & Kubernetes : HashiCorp's Vault and Consul - Auto-unseal using Transit Secrets Engine - 2020
Inconsistencies in Transit engine for keys read & export operations · Issue #10352 · hashicorp/vault · GitHub
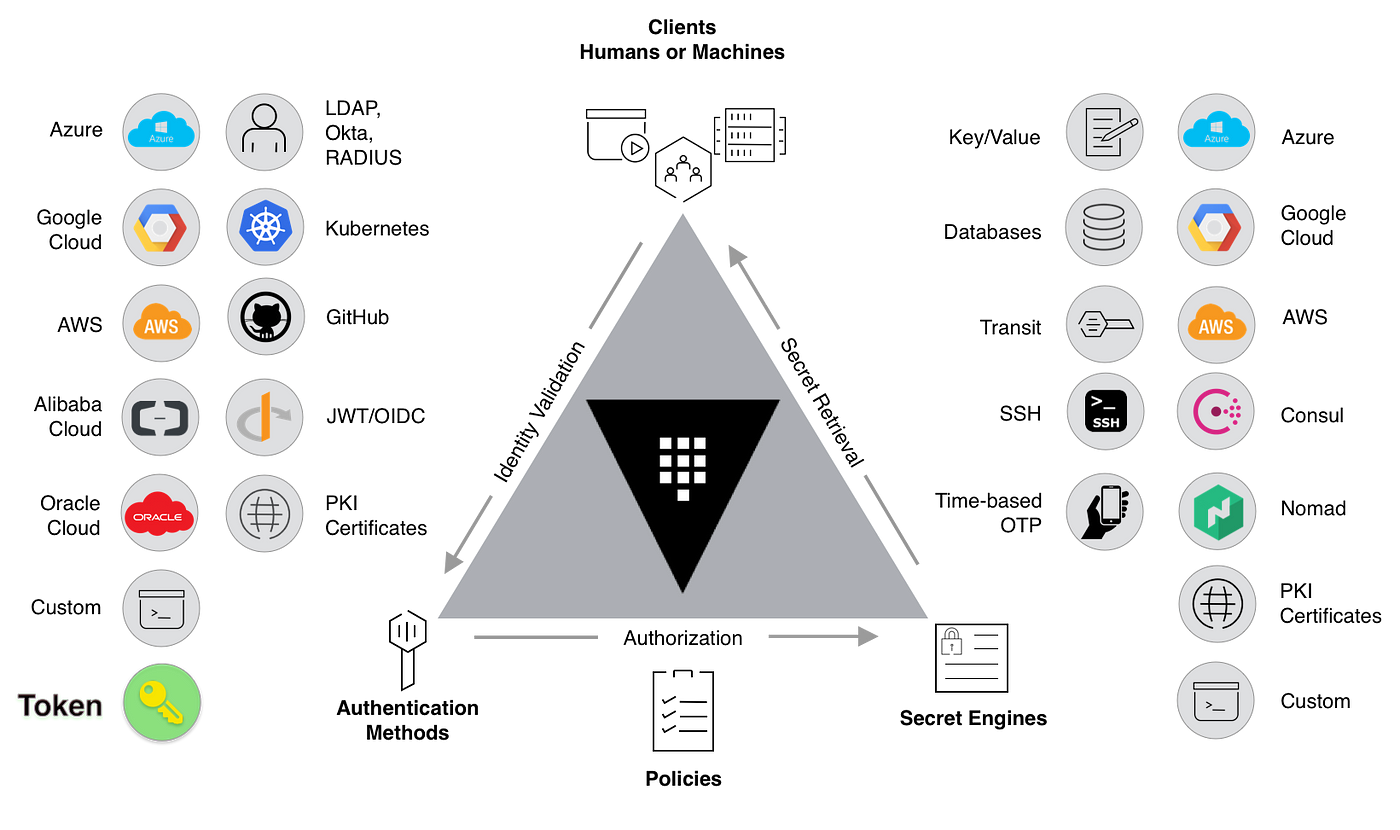
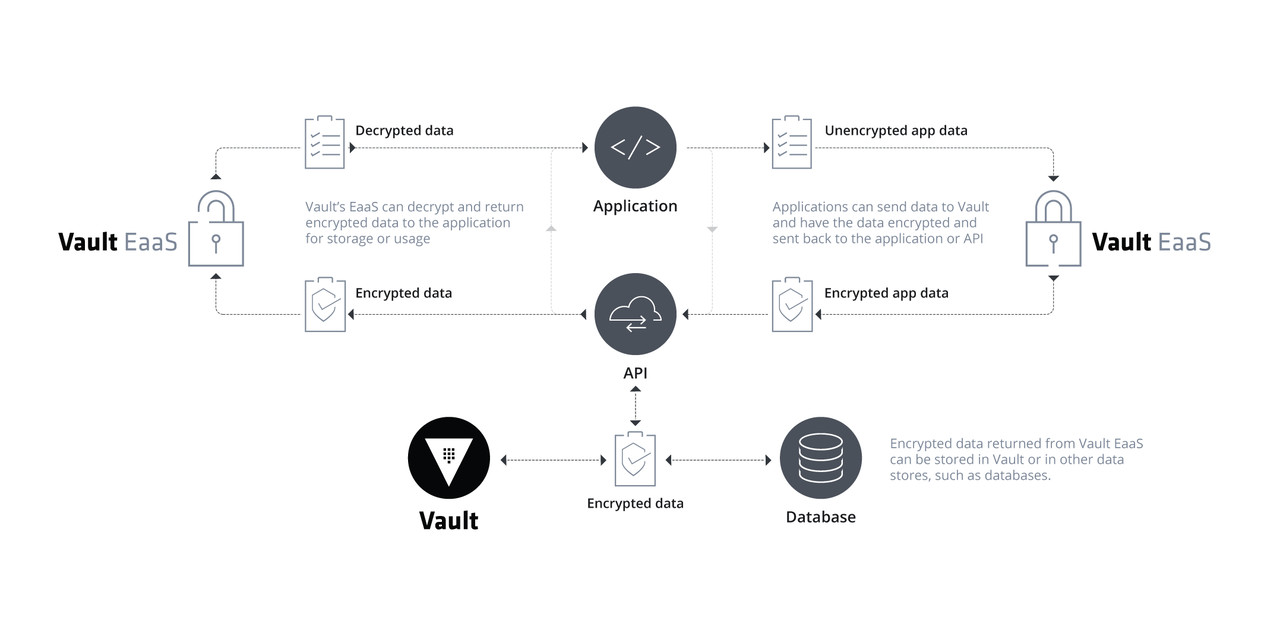
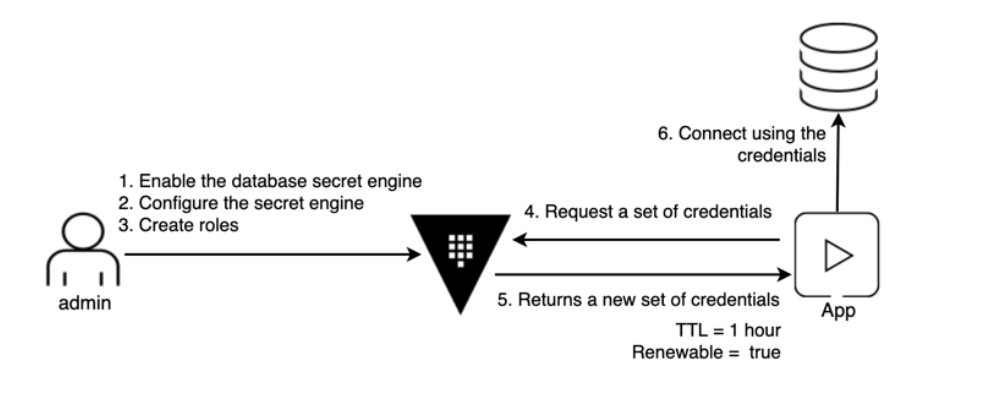
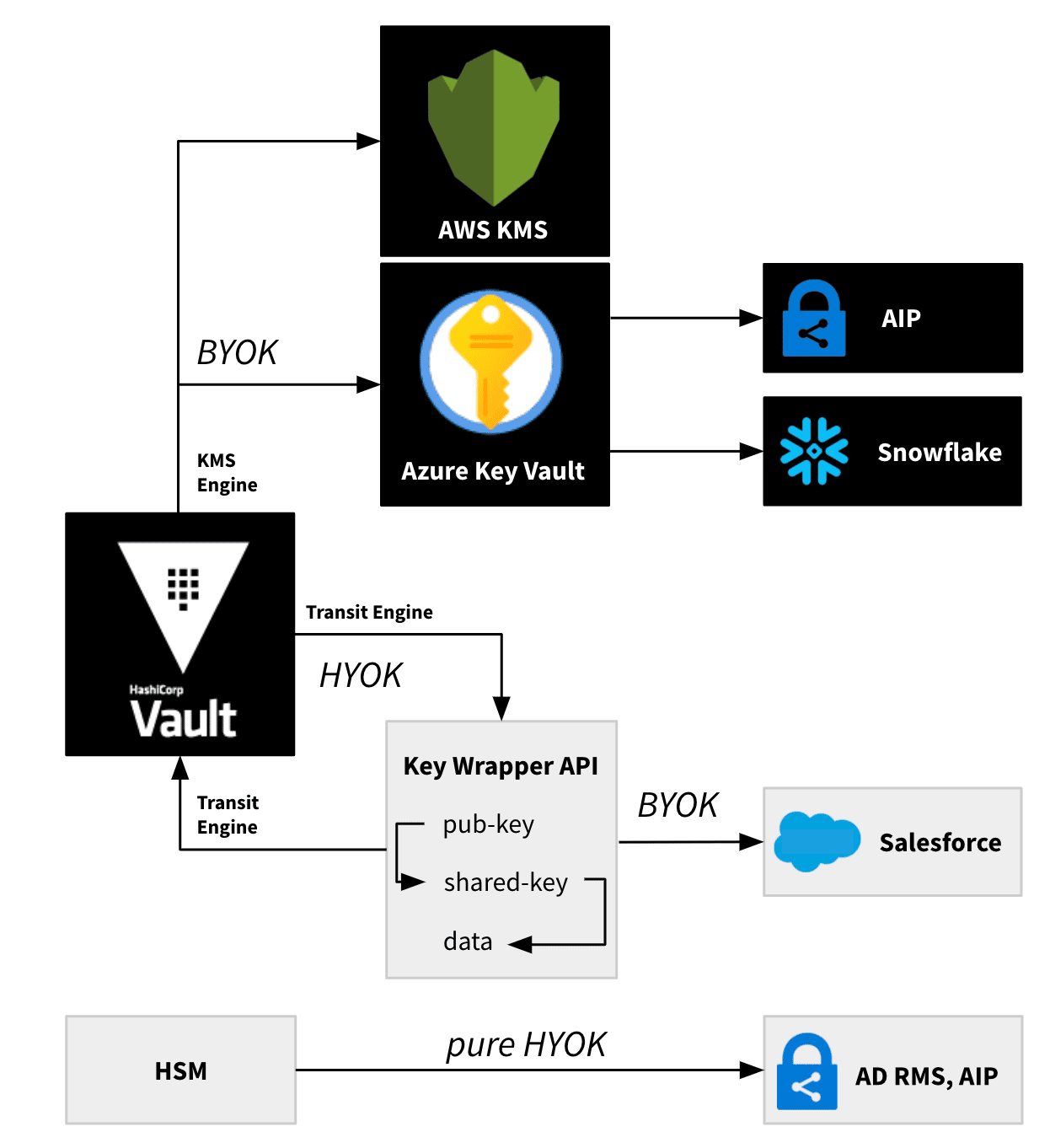
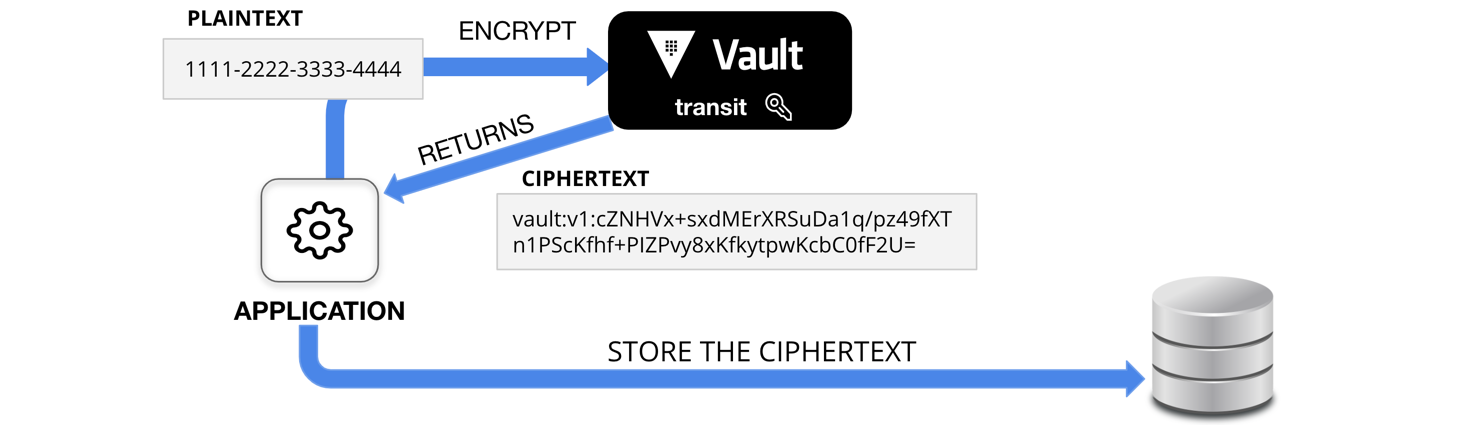
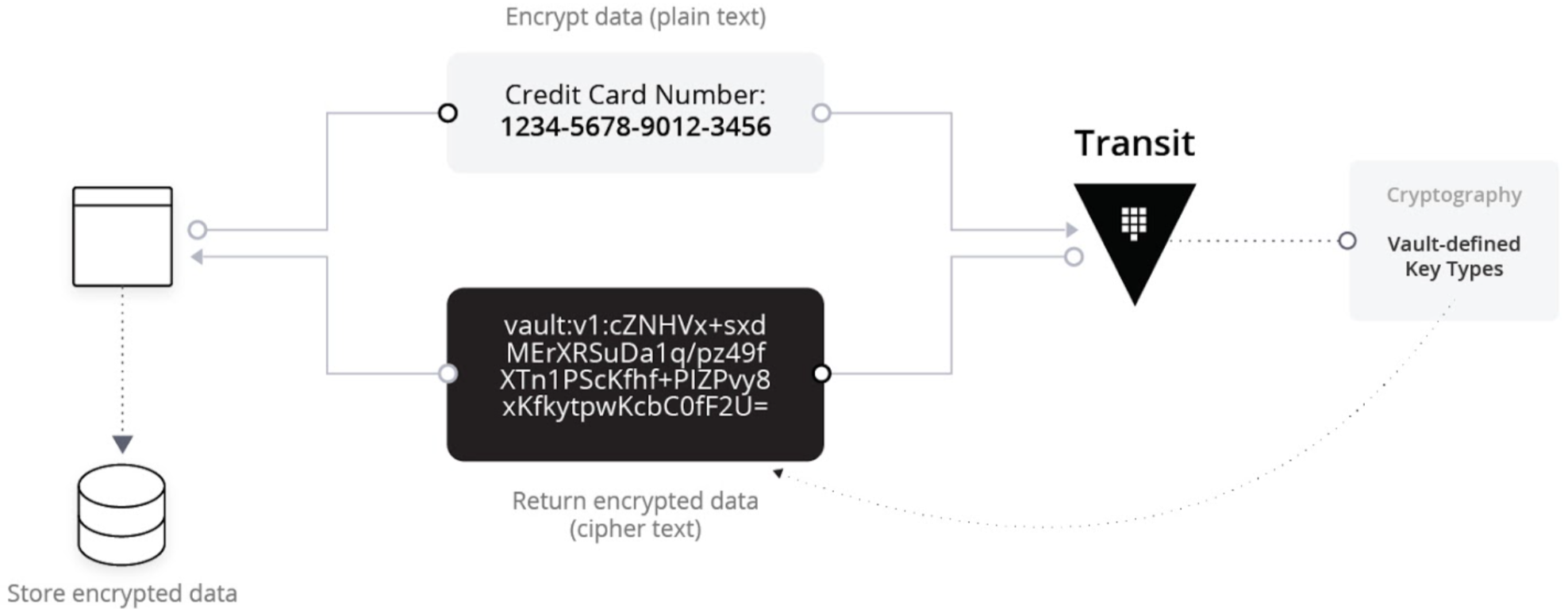
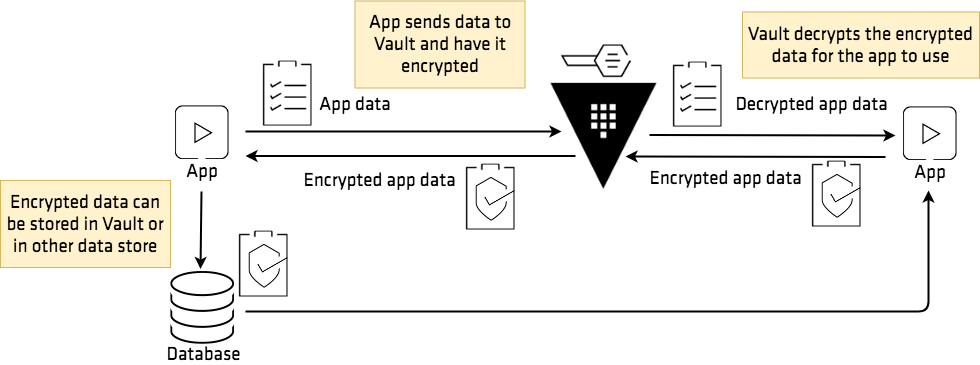
Essential Patterns of Vault — Part 2 | by Jake Lundberg | HashiCorp Solutions Engineering Blog | Medium
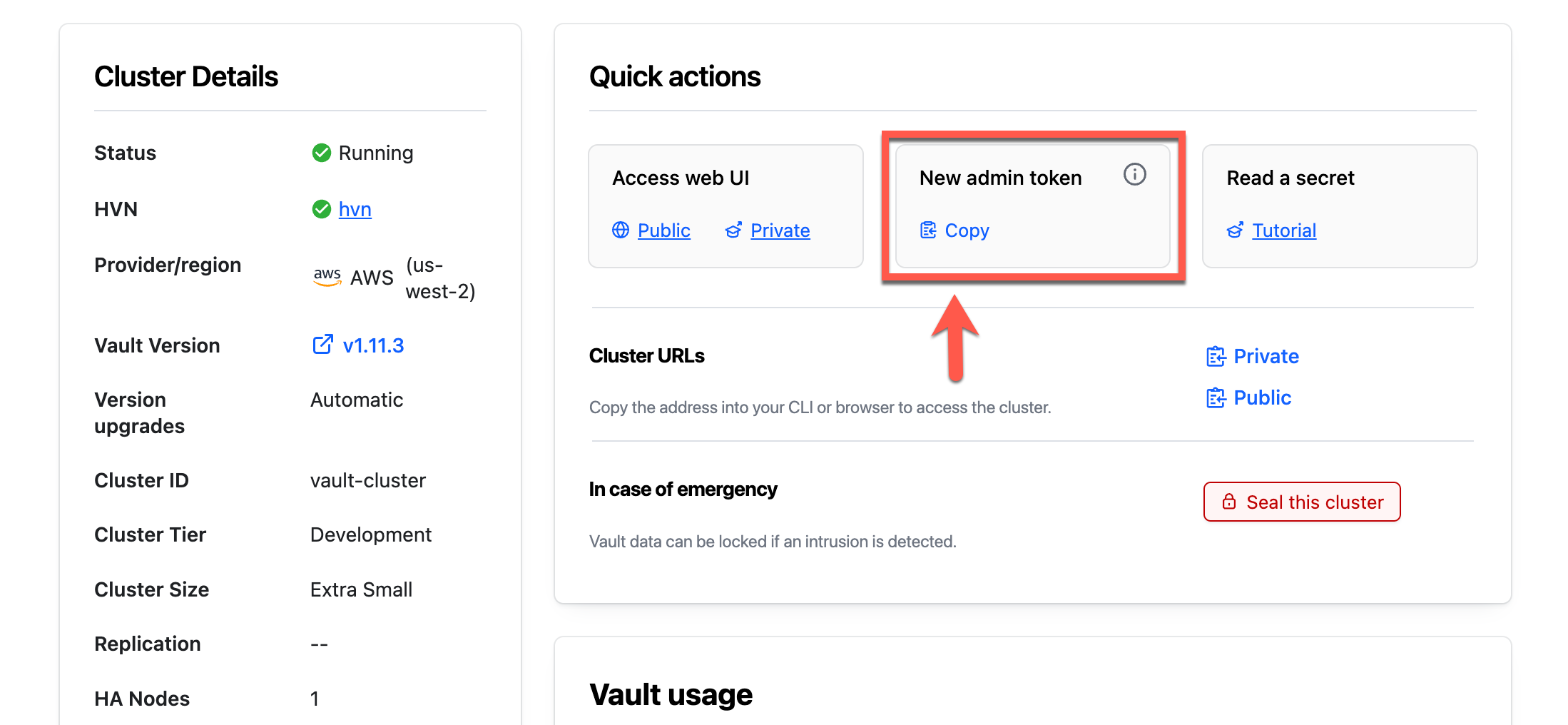
Deploy HCP Vault & AWS Transit Gateways via Terraform | by Andrew Klaas | HashiCorp Solutions Engineering Blog | Medium