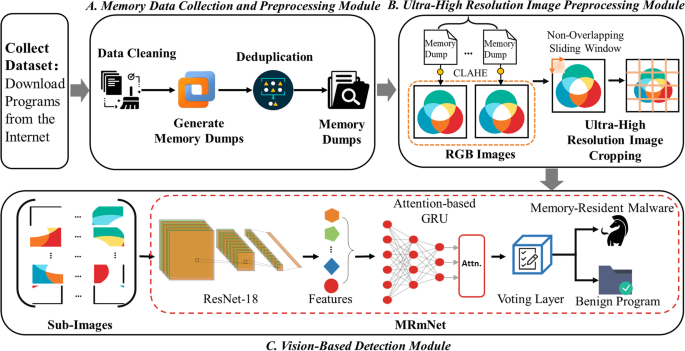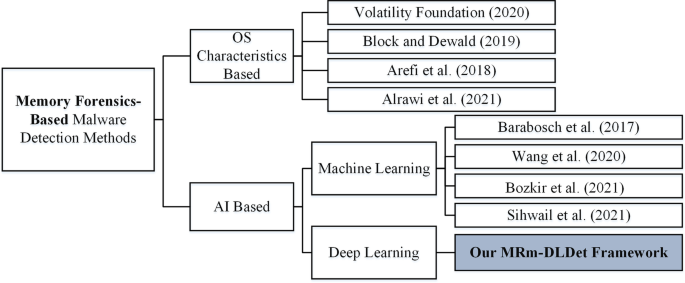
MRm-DLDet: a memory-resident malware detection framework based on memory forensics and deep neural network | Cybersecurity | Full Text
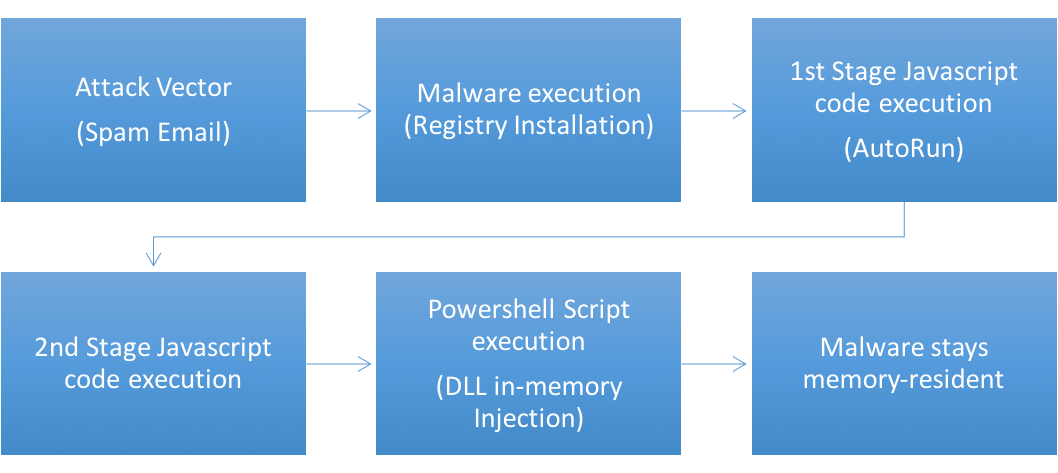
Shelltea + Poslurp Memory-Resident Point-Of-Sale Malware Attacks Industry | Cyentia Cybersecurity Research Library

MRm-DLDet: a memory-resident malware detection framework based on memory forensics and deep neural network | Cybersecurity | Full Text

The Art of Memory Forensics: Detecting Malware and Threats in Windows, Linux, and MAC Memory : Ligh, Michael Hale, Case, Andrew, Levy, Jamie, Walters, Aaron: Amazon.it: Libri

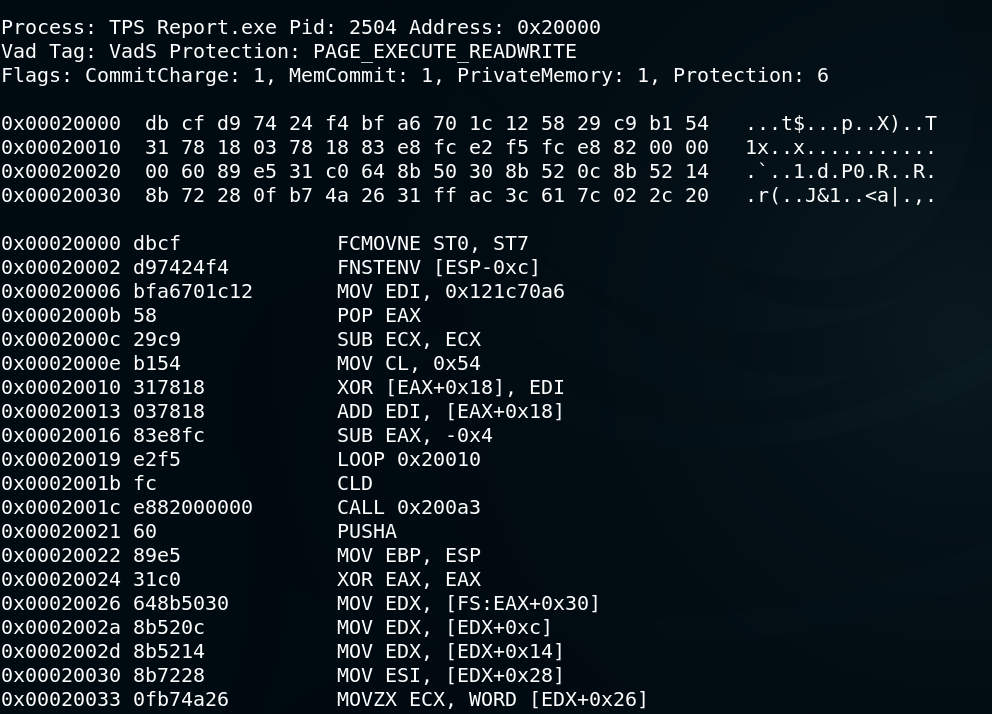
Hunting for Memory-Resident Malware - Joe Desimone Derbycon 2017 (Hacking Illustrated Series InfoSec Tutorial Videos)

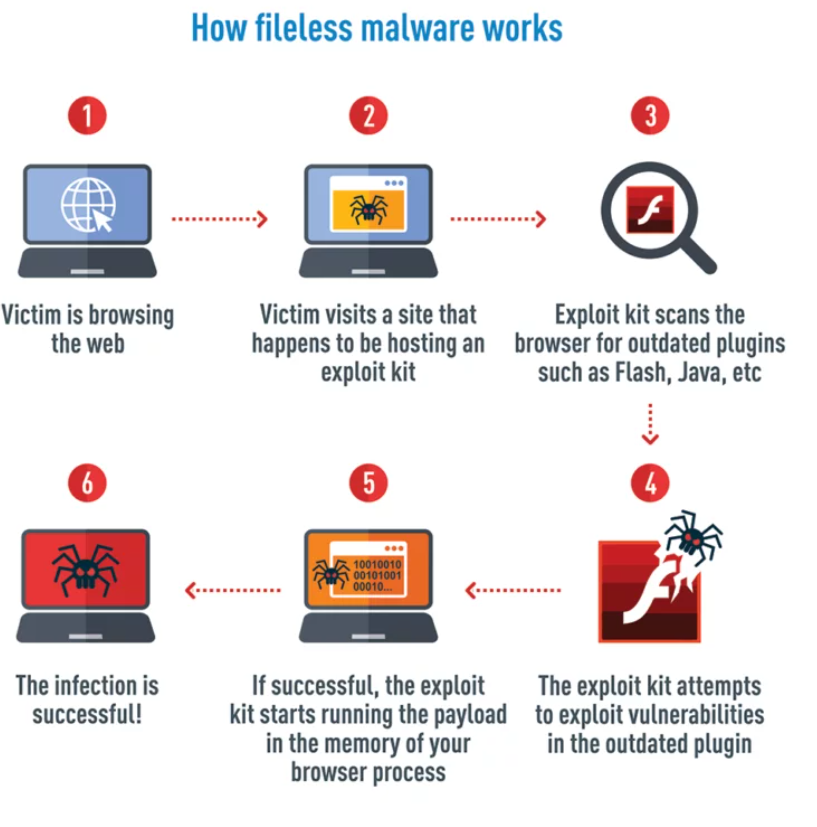
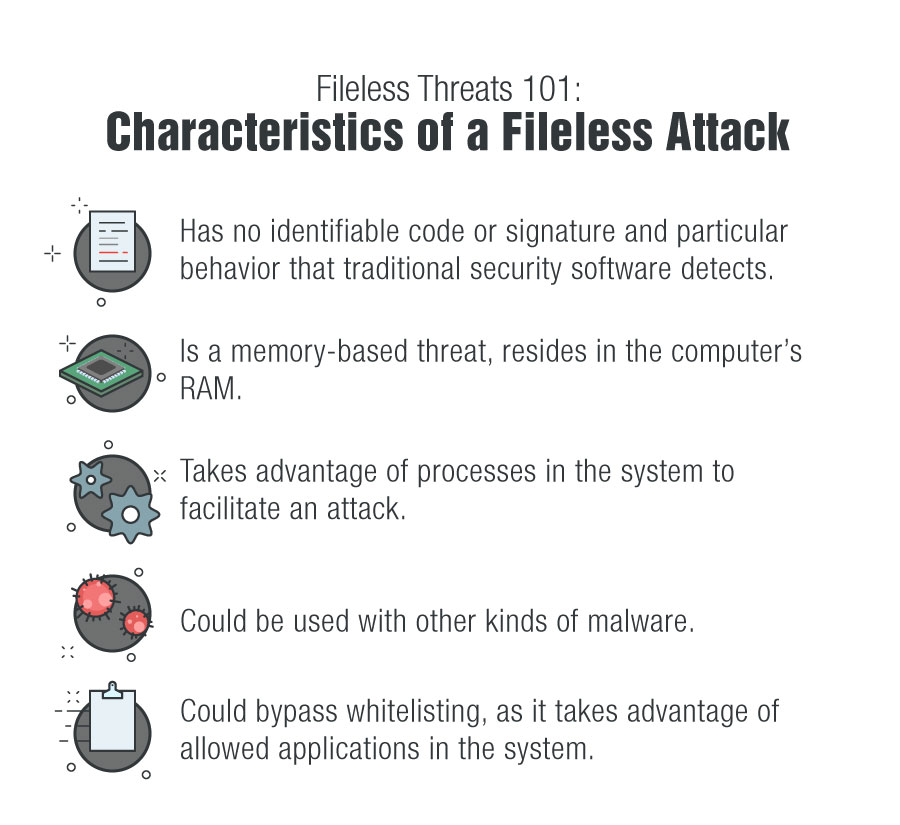
Memory-Resident Malware: What You Should Know - Logix Consulting Managed IT Support Services Seattle

Infographic for How To Prevent Memory Resident Virus with Memory Chip, Magnifier and Warning Symbol - Isolated on Light Background Stock Vector - Illustration of graphic, internet: 180788479

Carlos Garay - Memhunter Automated Hunting Of Memory Resident Malware - DEF CON 27 Blue Team Village